In a notable regulatory pivot, the U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) has rescinded sanctions targeting Tornado Cash, an Ethereum-powered service for algorithmic mixing of digital assets, reigniting discourse about its operational integrity. Even as legal barriers dissolve, industry observers and digital defense professionals urge extreme caution against using the platform.
OFAC Unshackles Tornado Cash—But Security Hawks Warn: Frontend Remains a Minefield
This article was published more than a year ago. Some information may no longer be current.

Experts Insist Tornado Cash Frontend Risks Still Remain
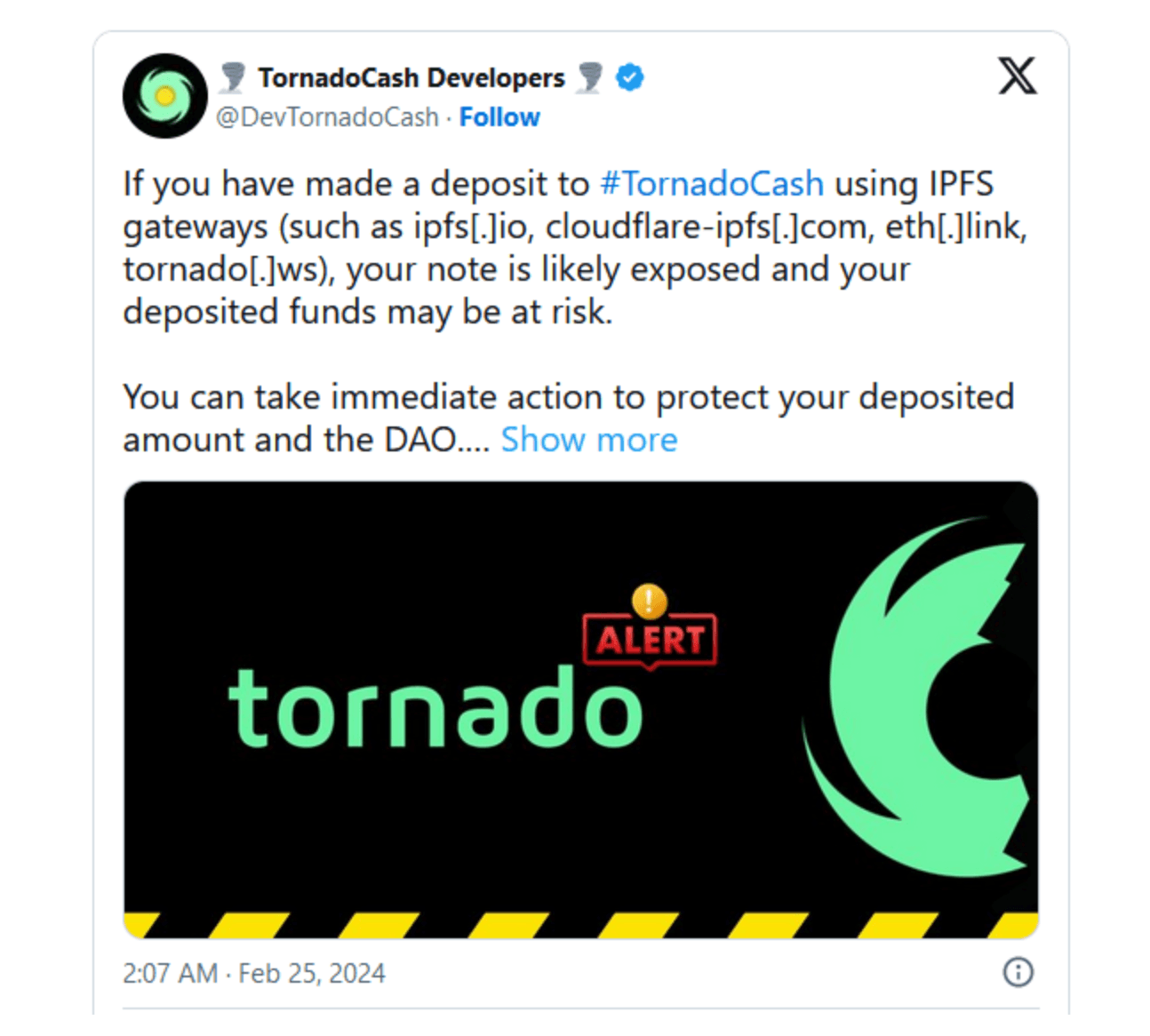
Blockchain forensic experts and crypto proponents highlight a February 2024 episode in which adversaries allegedly injected malicious Javascript scripts into Tornado Cash’s governance proposal infrastructure.
This intrusion—which leveraged decentralized storage gateways to siphon user assets—exposes a pressing weakness, eroding confidence in the platform’s defenses despite its revived legal standing.
This development trails OFAC’s Friday announcement removing economic restrictions against Tornado Cash. The U.S. agency disclosed a formal communication confirming the platform’s removal from its sanctions registry.
While pledging ongoing scrutiny of transactional activity, the Treasury simultaneously released an expansive registry of previously blacklisted entities, including Tornado Cash and an array of associated cryptocurrency wallets.
“For those who will start using Tornado again remember that the main frontend is still compromised,” onchain detective ZachXBT cautioned hours after OFAC removed the Ethereum-based mixing service from its sanctions roster.
Observers highlighted Tornado Cash’s open-source architecture, suggesting users could independently deploy its front-end interface, while some proponents distributed hardened IPFS hashes to sidestep vulnerabilities.
Nevertheless, a chorus of experts urged vigilance, framing engagement with the protocol as a potential forfeiture risk of digital holdings should its lingering vulnerabilities materialize.

















