Seventeen and a half million Instagram accounts just got an unwanted encore appearance on the dark web, thanks to an old API flaw that’s back to cause fresh headaches.
Instagram Data From 2024 Leak Reappears, Exposing 17.5M Accounts

According to a security notice from cybersecurity firm Malwarebytes, data tied to roughly 17.5 million Instagram users is circulating freely on Breachforums after resurfacing in early January 2026, courtesy of a threat actor using the handle “Solonik.” The twist: this wasn’t a brand-new breach. The data reportedly traces back to a misconfigured Instagram API from late 2024 that allowed large-scale scraping of user profiles, quietly collecting structured information before disappearing—until now.
“Beware of emails and messages that claim to come from Instagram, as they could be sent by malicious hackers trying to trick you into handing over your password,” Malwarebytes explained in a distributed alert email. “If you’re concerned, sign into your Instagram account and reset your password to a new, strong, unique password.”
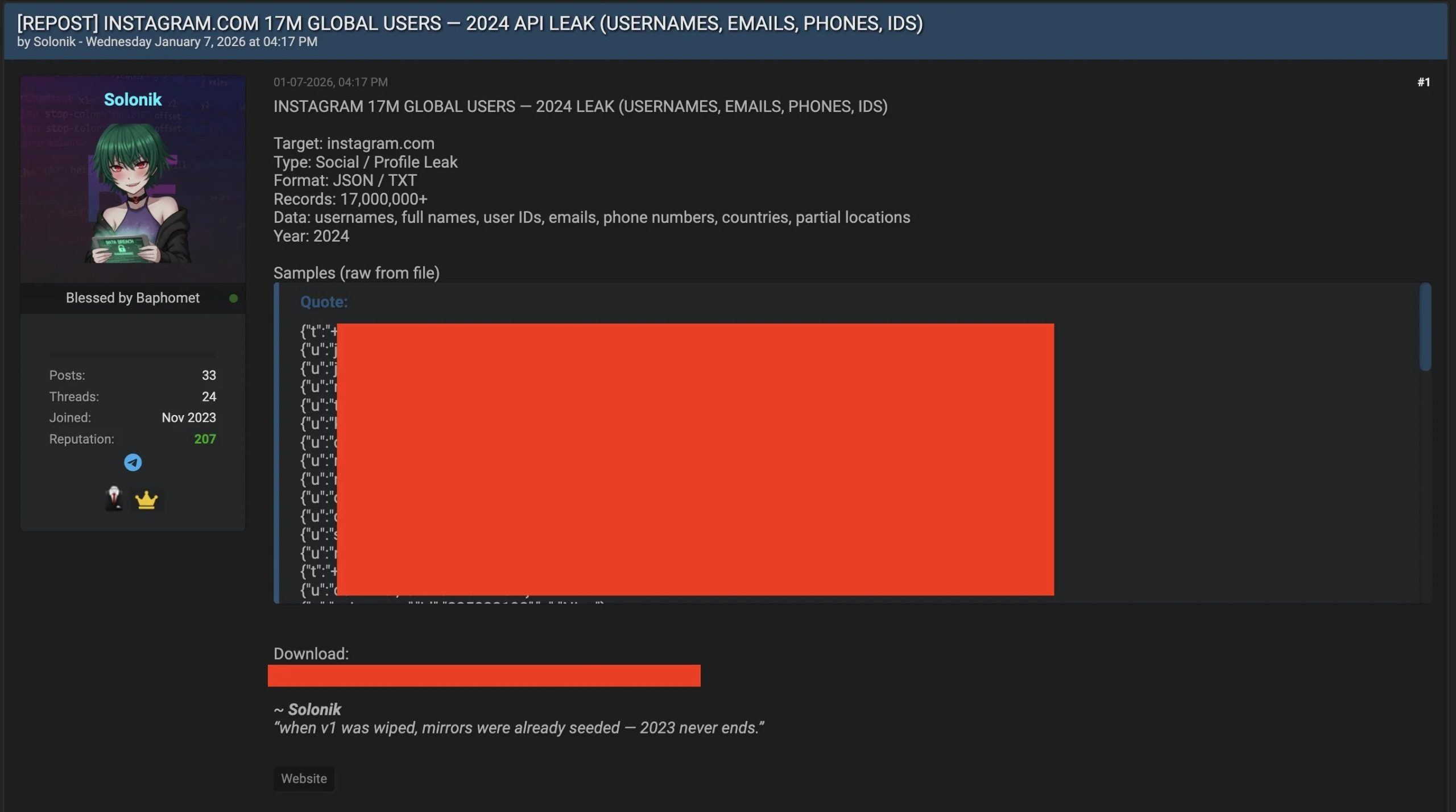
The freshly reposted dataset is said to include usernames, emails, phone numbers, physical addresses, and account metadata, making it catnip for scammers and identity thieves. As of Jan. 10, Meta had not issued a public statement, while reports of unsolicited password reset emails has spiked. Old data, new damage—because the internet never forgets, and neither do cybercriminals. What makes this leak especially irritating is how it’s being used.
Attackers aren’t blasting obvious scam emails; instead, they’re triggering legitimate Instagram password reset messages from the platform’s real security domain, banking on confusion to do the dirty work. With enough personal details in hand, bad actors can escalate from phishing to even SIM swapping and targeted fraud, particularly for users who recycle passwords across sites.
Malwarebytes flagged the breach during routine dark web monitoring, showcasing how recycled data can still fuel very current attacks. While the exposure appears global—with confirmed impacts in parts of Europe—the risk profile is universal: account takeovers, financial fraud, and a fresh reminder that scraped data ages like milk, not wine. The fix is unglamorous but effective: stronger passwords, two-factor authentication, and a healthy suspicion of any “urgent” email demanding clicks.
FAQ 🔒
- Was this a new Instagram hack?
No, the data reportedly originates from a 2024 API scraping issue and only resurfaced publicly in January 2026. - What information was exposed?
Usernames, emails, phone numbers, partial or full addresses, and account metadata were included. - Why are users getting real password reset emails?
Attackers are abusing Instagram’s legitimate reset system to make phishing attempts seem authentic. - What should affected users do now?
Change passwords immediately, enable two-factor authentication, and monitor accounts for suspicious activity.