Nick Johnson, a well‑known Ethereum Name Service (ENS) engineer, disclosed a cunning phishing campaign that preyed on weak spots within Google’s backbone, notably a recently patched OAuth flaw.
ENS Lead Developer Reveals Flaw Allowing Phishers to Mimic Official Google Alerts

Google’s Guard Down: ENS Engineer Tracks Phishing Exploit
The scheme, according to Johnson’s testimony, kicked off with a persuasive email, seemingly dispatched by an official Google alert, alerting targets to a subpoena demanding their account data. Signed with a genuine DKIM key and originating from Google’s official no-reply domain, the notice sailed past Gmail’s filters and nestled among legitimate alerts.
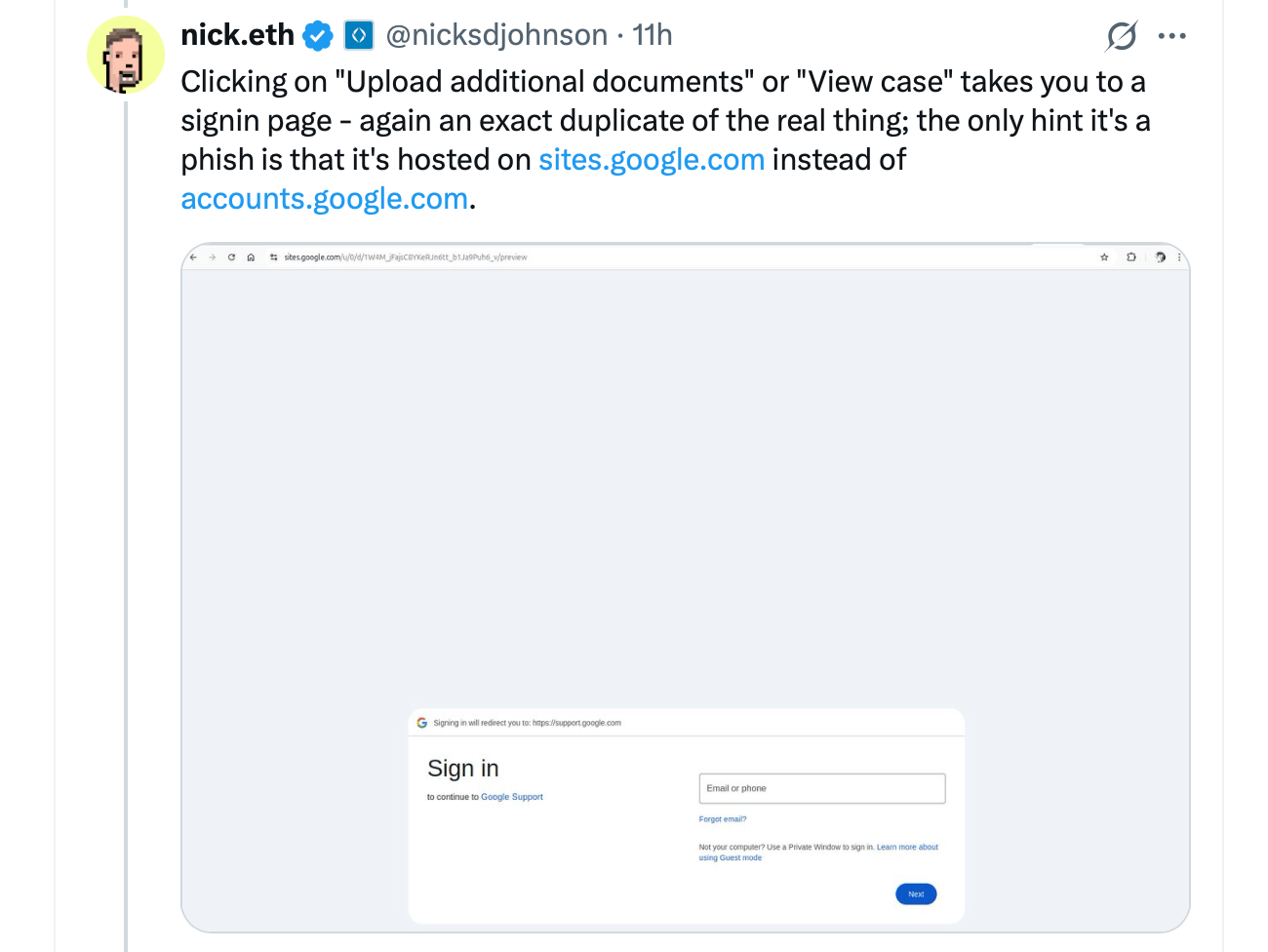
Johnson observed that its credibility was further lifted by a sites.google.com hyperlink leading to a counterfeit support portal that mirrored Google’s sign‑in page. The developer noted that the ruse leaned on two cracks: Google Sites’ tolerance for arbitrary scripts, which let criminals craft credential‑harvesting pages, and the OAuth weakness.
Attackers registered a fresh domain, opened a Google account, and built an OAuth application whose name duplicated the phishing email’s title. Once a victim granted access, Google automatically generated a security‑alert email—fully signed and legitimate—that the attackers then relayed to their quarry.
Johnson castigated Google for first brushing off the bug as “working as intended,” contending the loophole posed serious peril. The bogus portal’s reliance on sites.google.com further misled users because the trusted domain cloaked hostile intent. Weaknesses in Google’s abuse reporting for Sites deepened the trouble, slowing takedown efforts.
After public pressure mounted, Google pivoted and acknowledged the problem. Johnson later confirmed the tech firm plans to remedy the OAuth defect. The episode illuminates phishing’s growing finesse, exploiting revered platforms to slip past defenses.
Security specialists plead vigilance, urging users to question unexpected legal correspondence and double‑check URLs before typing credentials. Google has not yet issued a public statement on the flaw or its repair schedule. The case exposes the wider struggle against phishing as adversaries increasingly weaponize reputable services.



















