In the aftermath of the $1.4 billion cybersecurity breach targeting centralized digital asset platform Bybit, onchain evidence reveals that perpetrators have systematically converted a fraction of the pilfered funds into bitcoin ( BTC).
Cyber Thieves Convert a Segment of Bybit Loot Into Bitcoin
This article was published more than a year ago. Some information may no longer be current.

Hackers Mask Tracks by Moving Bybit Heist Funds to Bitcoin
This week, North Korea’s Lazarus Group orchestrated a cyber incursion against digital asset exchange Bybit, exfiltrating upwards of $1.4 billion in a brazen virtual heist. Blockchain investigator ZachXBT subsequently uncovered that the perpetrators funneled a portion of the ill-gotten assets into Pump.fun, a whimsically named meme coin launchpad.
Further analysis reveals the group diverted Ethereum holdings through decentralized cross-chain trading protocols, methodically converting them into bitcoin ( BTC)—a calculated maneuver to cloak their tracks within the cryptocurrency’s labyrinthine networks. Bybit’s CEO Ben Zhao revealed this info on the social media platform X.
“We are starting to see some funds being moved to [Chainflip.io] as bridge to convert to BTC: bc1qlu4a33zjspefa3tnq566xszcr0fvwz05ewhqfq,” Zhao said sharing the bitcoin address and swap transaction data. “If you are a bridge, please help us to block and prevent further conversion to other chains. We are going to release our bounty program very soon to whoever helps us to block or trace the funds that result in fund recovery,” he added.
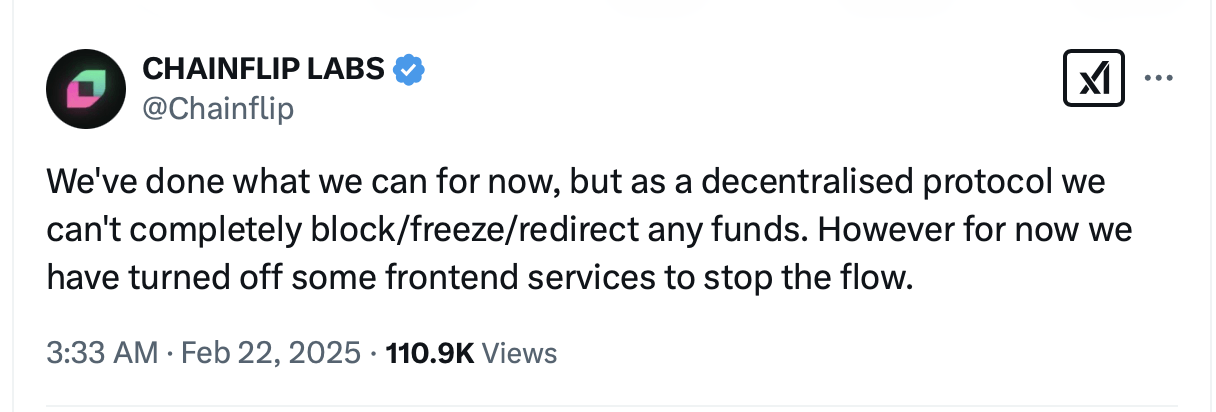
Chainflip outlined its limitations as a decentralized protocol, clarifying it cannot comprehensively immobilize assets due to its non-custodial architecture.
Meanwhile, analytical findings and blockchain forensics reveal pilfered capital was funneled through the digital exchange exch.cx (colloquially dubbed “Exch”), executing a ballet of cloaked maneuvers. Reports indicate Exch exhibited no collaboration efforts with Bybit’s investigators, even alleging the platform tarnished its “reputation.”
Blockchain security platform Slowmist’s Misttrack further documented Exch’s recurrent noncompliant posture toward blockchain forensic initiatives, painting a portrait of deliberate opacity. “Exch just publicly posted Bybit’s interception request email and issued a response,” Misttrack posted on X. “Not the first time—they’ve done the same to us and many other security researchers.” Zhao also brought up the issue with Exch on X.
“At this point is really not about Bybit or any entity, it’s about our general approach towards hackers as an industry, really hope that Exch can reconsider and help us to block funds outflowing from them,” Zhao wrote. “We are also getting help from Interpol and international regulatory bodies, helping block these funds is not just helping Bybit.”

















