It seems Tor is putting back up its defenses after discovering the FBI had broken through them earlier this year. According to a new paper, developers at the Tor Project have been working closely with security researchers to create a “hardened” version of the browser.
Tor Project Enlists Security Researchers to Counter FBI Snooping
This article was published more than a year ago. Some information may no longer be current.

Also read: Unconfirmed Transactions, Support & Open Dialogue
Tor Strikes Back
This “hardened” version of the Tor browser would entail stronger anti-hacking techniques that could frustrate the spying activities of the FBI and other various government agencies by improving the anonymity of the user.
The improvements are largely based upon a method dubbed “selfrando,” which was created to protect against browser exploits, including the one used by the FBI against the Tor browser.
The new method is meant to counteract “code reuse” exploits, where memory leaks allow attackers to reuse existing code libraries instead of injecting an entirely new malicious code. By employing code reuse exploits, attackers can build 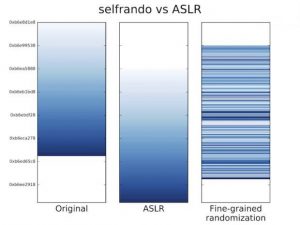 malware into the application by rearranging certain aspects of its memory.
malware into the application by rearranging certain aspects of its memory.
To do this, attackers usually need to have a general idea of where certain functions are within the application’s memory space. However, as it stands, current security measures in browsers only randomize the locations of code libraries and not their individual functions.
The Selfrando technique changes all of this by creating a random address space for internal code that’s harder to exploit.
This means if this “Selfrando” method works out, then it is going to become much harder to hack Tor — drastically swinging the cybersecurity advantage to the Tor browser.
A Promising Future Ahead
When the news first hit that the P2P network had been compromised by the FBI, there were many in the Bitcoin community who were understandably upset. This reaction was not surprising considering the software is often used to supplement the anonymity inherent to the Bitcoin network.
It probably didn’t provide much solace to Bitcoiners knowing that the so-called Torsploit malware was partially the responsibility of a former Tor developer. Regardless, the incident was a major blow to anyone who used the anonymity software.
Fortunately, it seems the Tor project is on the right path to seal the backdoor created by the FBI, and in doing so will restore integrity back to the network, even if only temporarily.
What do you think of Tor’s new anti-hacking technique? Let us know in the comments below!
Source: Motherboard
Images courtesy of DeepDotWeb, Tor.