In 1992, the Internet became more accessible to the public. With this advancement, NSA activities kicked into full force, foreshadowing their present-day activities. Using techniques to invade privacy and create a monopoly of mass data collection, the NSA’s secrets have been exposed by whistleblowers. Most notably, former NSA employee Edward Snowden has deeply exposed the NSA, forcing him to flee the US. Revelations brought to the table by Snowden have revealed that NSA spying has been immense, global, and continues to invade our private lives. Prior to that turning point in 1992, a group of young software developers and visionaries stepped into the spotlight to battle against this kind of invasion, creating educational papers and protocols to fight these attacks.
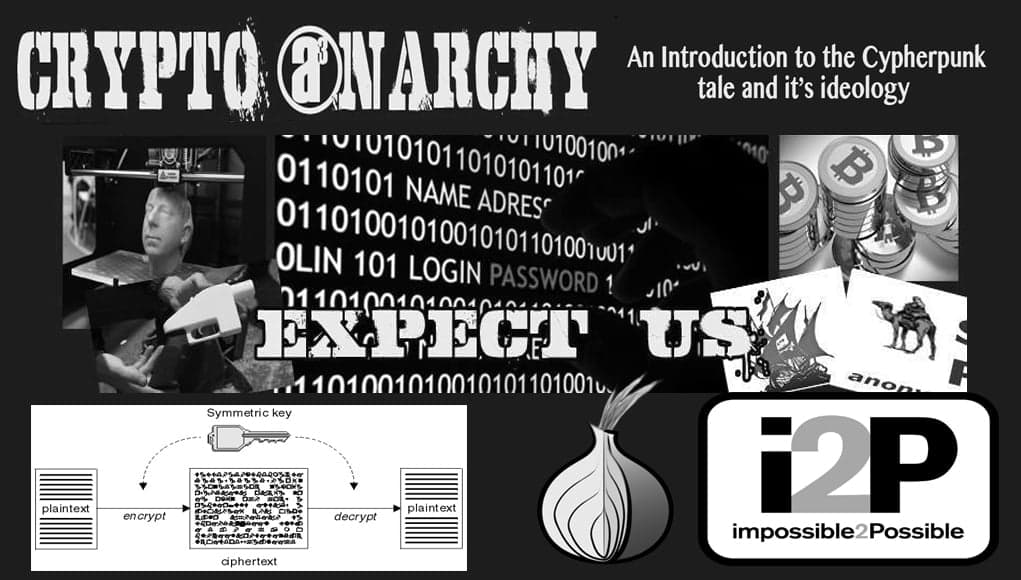
An Introduction to the Cypherpunk Tale
This article was published more than a year ago. Some information may no longer be current.
The NSA has built an infrastructure that allows it to intercept almost everything. With this capability, the vast majority of human communications are automatically ingested without targeting. If I wanted to see your emails or your wife’s phone, all I have to do is use intercepts. I can get your emails, passwords, phone records, credit cards. — Edward Snowden
The Cypherpunks’ ideas were born in the heart of Silicon Valley with the vision of protecting privacy and promoting liberty by using technology. A cypherpunk is an activist who uses software, protocol, and most importantly cryptography to invoke social and political change. A few decades ago, the NSA and military had a monopoly-like control over the field of computational cryptography. It wasn’t until 1975, when Whitfield Diffie created “public-key” cryptography, that the monopoly was broken in the eyes of many. Public-Key cryptography pushed forth a new era of activism through the use of technology. This new form of cryptography led to the creation of private mailing lists, software to protect individuals, data houses, and cryptocurrency.
In the early nineties, a group of these activists formed the “Cypherpunk Mailing List” to exchange information on privacy, cryptography and online liberty. Started by Timothy May, Eric Hughes, St. Jude and John Gilmore , the group officially started out pretty small. This group of individuals used to meet publicly every Saturday at a small office in the heart of Silicon Valley. Over time, the online mailing list grew with heavy contributions from the likes of Julian Assange, Adam Back, Phil Zimmerman, and Hal Finney. Each and every member added value to protect online privacy in the new technological economy, advancing individual methods to battle government intrusion.
Tim May, the founding member of the cypherpunks, wrote many political writings explaining the role of the group to the online community. As a senior scientist for Intel, May used his spare time to write about the importance of cryptography as a tool to protect user information. May created material such as the “Crypto-Anarchist Manifesto,” the “Cyphernomicon,” and “Crypto Anarchy-Cyberstates and Pirate Utopias.” These essays explained the vision of May’s ideology and served as a preamble for things to come. Many of the spoken elements in his work came to life throughout the following decade.
May revealed the “Crypto-Anarchist Manifesto,” in 1992, reading his work at the founding meeting of the Cypherpunks. He said that the essay itself had manifested in 1988 and he distributed the work at the “Hackers Conference” that year. The essay described the many advances in technology that could possibly be used to thwart off the invasion of privacy by the state and its tethered entities. May explained that computational protocols were on the verge of giving individuals and groups control over their online identities — allowing individuals to communicate and exchange anonymously. He explains:
Interactions over networks will be untraceable, via extensive re- routing of encrypted packets and tamper-proof boxes which implement cryptographic protocols with nearly perfect assurance against any tampering. Reputations will be of central importance, far more important in dealings than even the credit ratings of today. These developments will alter completely the nature of government regulation, the ability to tax and control economic interactions, the ability to keep information secret, and will even alter the nature of trust and reputation. — Tim May, 1992
When read today, many wonder how this wild piece of information predicted great technological events such as the advances in Tor, I2P, and cryptocurrency. How decades earlier, May was able to envision such advanced uses of technology during the early days of cyberspace. He said that, of course, the State would try and hinder such a spreading of technological information by creating false “protection” concerns for users of the net. May cited things such as drugs and tax evasion as examples of the government’s reasoning for “protectionism.”
However, May said that the State’s concerns would become “valid,” as the hope of the Cypherpunk ideology was to promote these very things. Such expressions of intentionality — considered unethical to some — were promoted regularly by May and his group of hackers. The groups was especially interested in the idea of pure and unaltered privacy, money laundering, and ultimate technological disruption.
Tim May and his group of “Crypto-Robin Hooders” gave life to the power of cryptography, anonymity, and the exchange of cryptocurrency with their words and software development. They simply spoke and gave the tools to help protect groups and individuals in the early 90s; this ideological torch was carried by later generations following their activism.
Since 1992, disruption and disobedience through cryptography has advanced so rapidly that it’s hard to imagine these people envisioned it over 20 years ago. Yet, they didn’t just envision the environment, they created the tools to implement this revolution.
Crypto-Anarchy is alive and well. It thrives in between the websites and online chat rooms we visit everyday. May and his band of revolutionaries have changed the paradigm of thought for many and created the Pirate Utopias we all use to battle the tentacles of the state apparatus. Concepts like Bitcoin, Tor, and crypto-parties are very prevalent movements in our online society.
Marketplaces like the Silk Road have proven to be invaluable to Cypherpunks of this new age. When destroyed by governments, these markets appear again in mass quantities like a game of “Whack-A-Mole.” It is impossible to destroy an idea. The State tried to do so with the Silk Road, shutting down its servers and arresting its employees. However, the idea and concepts have not vanished from the online community, but have grown stronger. May provided people with these visions of decentralized marketplaces in times when Tor and Bitcoin did not exist. He told us the time has come to clip the barbed-wire fences of intellectual property — and it’s happening:
Privacy is necessary for an open society in the electronic age. Privacy is not secrecy. A private matter is something one doesn’t want the whole world to know, but a secret matter is something one doesn’t want anybody to know. Privacy is the power to selectively reveal oneself to the world. — Eric Hughes
A specter haunts us right now, and the ideals of the early Cypherpunks are being embraced daily. With its visions expressed in the early days of cyberspace, the sky appears to be the limit in this technological war against the State. A new day is rising where information spread by the likes of these Cypherpunks encompasses our everyday lives. Governments cannot stop this dissemination of information; when they try, it only shows their corruption more. In time, decentralization will make the vision of authority so blurry that a true distributed consensus in society is all we shall see.
The future is bright. Get out those clippers!
What do you think the tools of the Cypherpunks will do to society? Let us know in the comments below.















