In this day and age online privacy and protecting digital data is a pretty big deal. Privacy applies to bitcoin users even more so because they are storing wealth in the digital realm. Governments, hackers, and non-state actors are compromising global citizens private data daily, but there are many steps one can take to protect oneself.
How to Protect Your Bitcoin Privacy and Security Online
This article was published more than a year ago. Some information may no longer be current.

Currently, the world is threatened by global mass surveillance from countries participating as the “fourteen eyes,” an alliance of fourteen countries sharing intelligence and people’s data on a global level. Privacy has been attacked by the state, and non-state actors and analysts suggest this will only increase over the years. Within the online world, there are many tactics users can utilize to protect themselves from unwanted snooping.
Also read: John McAfee: Wake the F*** up to Consumer Security Threat
Three Methods That Protect Privacy Online
Privacy-Centric Web Browsers
 There are a few web browsers that offer better privacy than standard browsers traditionally used by the mainstream. The open source Brave browser is a great tool to block ads and tracking applications. The platform also uses bitcoin incentives to create a better experience. Another recommended browser for privacy is Mozilla’s Firefox which provides confidentiality and security focused extensions. If a person wishes to become even more anonymous then using Tor is a solid choice that hides IP, obfuscates proxies, and encrypts certain aspects of the browsing experience. In addition to the added privacy, Tor allows users to surf websites that are not indexed by Google and traditional browsers.
There are a few web browsers that offer better privacy than standard browsers traditionally used by the mainstream. The open source Brave browser is a great tool to block ads and tracking applications. The platform also uses bitcoin incentives to create a better experience. Another recommended browser for privacy is Mozilla’s Firefox which provides confidentiality and security focused extensions. If a person wishes to become even more anonymous then using Tor is a solid choice that hides IP, obfuscates proxies, and encrypts certain aspects of the browsing experience. In addition to the added privacy, Tor allows users to surf websites that are not indexed by Google and traditional browsers.
Virtual Private Networks (VPN)
 VPNs offer encryption and re-routing practices to change a user’s server location and IP address. Third parties are unable to track the exact location of a VPN user or monitor traffic if the product does what it claims. Make sure you are using a trusted VPN provider as each service offers a different experience and cost. Typically free VPNs are not recommended and researching a vendor is a must. Some services also offer a “logless” feature which ensures even the provider has no access to user data and traffic movements.
VPNs offer encryption and re-routing practices to change a user’s server location and IP address. Third parties are unable to track the exact location of a VPN user or monitor traffic if the product does what it claims. Make sure you are using a trusted VPN provider as each service offers a different experience and cost. Typically free VPNs are not recommended and researching a vendor is a must. Some services also offer a “logless” feature which ensures even the provider has no access to user data and traffic movements.
Privacy-Focused Email Services & Messaging
 There’s a wide variety of email and messaging services that offer strong privacy and end-to-end encryption. For email services such as Protonmail, Tutanota, OpenMailBox and many others offer encrypted email features. Users can use an OpenPGP encryption standard with their current email service. This type of method provides email encryption, decryption with shared keys, and digital signatures.
There’s a wide variety of email and messaging services that offer strong privacy and end-to-end encryption. For email services such as Protonmail, Tutanota, OpenMailBox and many others offer encrypted email features. Users can use an OpenPGP encryption standard with their current email service. This type of method provides email encryption, decryption with shared keys, and digital signatures.
End-to-end encrypted instant messaging services are also useful to stay private. Services such as Signal, Chatsecure, Telegram, and Ricochet offer different types of private messaging. Users surfing with the Tor browser can utilize TorChat which offers peer-to-peer encrypted messaging.
Cryptocurrency Security
For those who use cryptocurrencies over the web, security is integral to digital asset storage. Malicious hackers are gaining access to people’s wealth every day with people who don’t take responsibility securing their digital currencies. Cryptocurrency theft becomes more common with attackers utilizing social engineering methods to acquire people’s funds online.
Cold Storage
 Using cold storage practices is an excellent way to keep intruders out of your digital assets. The method entails keeping cryptocurrencies offline and out of harm’s way. Bitcoin and altcoin proponents can store offline using paper wallets, hardware wallets, and other forms of protected media. If you are not using your digital currencies daily then keeping them offline would be the safest choice rather than leaving them exposed on the open web.
Using cold storage practices is an excellent way to keep intruders out of your digital assets. The method entails keeping cryptocurrencies offline and out of harm’s way. Bitcoin and altcoin proponents can store offline using paper wallets, hardware wallets, and other forms of protected media. If you are not using your digital currencies daily then keeping them offline would be the safest choice rather than leaving them exposed on the open web.
Multi-Signature Transactions
Multisignature (multisig) is a method of using more than one person and keys to authorize a cryptocurrency transaction. The practice is a digital signature scheme that protects assets from being spent without the entire party of signers involved. Bitgo revealed the first multisignature wallet in 2013 and there are other variations available to the public. In essence, a multisignature address contains several ECDSA private keys, and all of them are needed to perform a transaction.
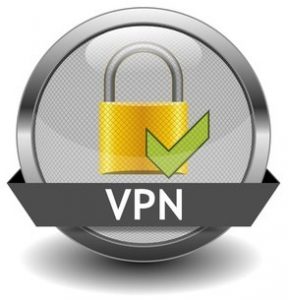
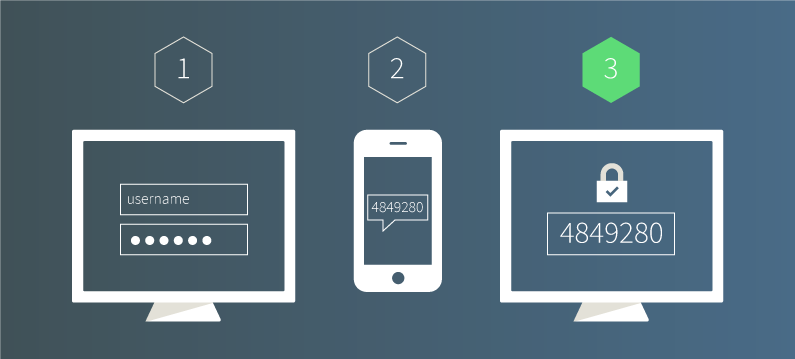
Multi-factor authentication (MFA) and Two-factor authentication (2FA)
MFA and 2FA are typical standard practices for most bitcoin users. The method confirms the identity of a user by using multiple verifications. Google Authenticator and Authy are well-known services that offer multiple validations. Bitcoin companies like exchanges and wallet services also offer SMS codes to use as 2FA to access their services. Adding MFA and 2FA features to bitcoin applications and accounts is highly recommended. Additionally securing your email that is tethered to an account also protects from malicious social engineering to accounts linked to your email.
Backing Up and Securing Seeds, PINs, and Passphrases
Most all of these services that ensure privacy and security use passphrases, mnemonic seeds, and PIN numbers to gain access. Backing up these details, so they don’t get lost or forgotten is a good idea. Users should keep copies of handwritten passwords and manage their entry data in a secure location typically offline. If a hardware wallets seed is lost or an account password is forgotten, sometimes people can be totally locked out from their accounts. There is a lot of debate over whether or not password managers are secure and if this type of application is used as a back a user should research with due diligence.
Also read: ‘No More Ransom’: A Summer Ransomware Project by Tech Security Giants
With Research Privacy and Security Can Be Obtained Within the Online World
There are many more methods of privacy and protection that can be used online and with cryptocurrencies. Researching and practicing these techniques will help ensure your digital footprint will not be tracked or attacked in an unfortunate way. There are many types of entities who find your digital data valuable. This means quite a bit of online experiences are manipulated in order to obtain your credentials and information. However protecting yourself from nosy governments and hackers looking to liquidate your wealth can be achieved.
What types of privacy and security methods do you use online and with cryptocurrencies? Let us know in the comments below.
Images courtesy of Shutterstock, Google images, and Pixabay.
Have you seen our new widget service? It allows anyone to embed informative Bitcoin.com widgets on their website. They’re pretty cool, and you can customize by size and color. The widgets include price-only, price and graph, price and news, forum threads. There’s also a widget dedicated to our mining pool, displaying our hash power.