Michael Richo waived his right to be indicted and pleaded guilty in a Connecticut courthouse on June 27 for charges related to operating a dark web phishing scheme. He pleaded guilty to money laundering charges and charges of fraud. Richo was originally arrested on October 5, 2016, in connection with the crimes. In the scheme, Richo stole user logon credentials and siphoned bitcoin from multiple dark web accounts. The amount was estimated to be worth about $365,000 in bitcoin.
How Michael Richo Stole Bitcoins via Imposter Exchange Sites and Dark Web Phishing Schemes
This article was published more than a year ago. Some information may no longer be current.

Also read: Asus and Nvidia Announce Purpose-Built Cryptocurrency Mining GPUs
The Scheme; Guilty Plea
Richo conducted the scheme via the tor network, and created  fraudulent business pages similar to known ones, where he would incite victims to sign up to those pages with a name and password. Then he would lay in wait until users logged in so he could steal their credentials.
fraudulent business pages similar to known ones, where he would incite victims to sign up to those pages with a name and password. Then he would lay in wait until users logged in so he could steal their credentials.
He would slyly watch accounts for newly deposited bitcoin. Once the unsuspecting victims deposited some amount, he would drain it into his own account. The Connecticut court documents detailed what he did with the stolen bitcoin:
“If the individual later also deposited bitcoins with the real marketplace, Richo withdrew the bitcoins before the individual could spend them and caused the stolen bitcoins to be deposited into his own bitcoin wallet. Richo then sold the stolen bitcoins to others in exchange for U.S. currency, which was deposited into bank accounts that Richo controlled or was provided to him through Green Dot Cards, Western Union transfers, and MoneyGram transfers.”
In the end, Richo pleaded guilty to one count of access device fraud and one count of money laundering. According to the court affiliated page, the fraud charge carries a minimum sentence of 10 years, and the money laundering charge carries a minimum of 20 years in prison. Documents stated Richo obtained more than 10,000 user credentials during the time of the phishing operation.
Rise in Bitcoin-Targeted Phishing Attacks
However, this type of phishing scheme does not only target users on the dark web to steal their bitcoin. Clearnet users also have to be wary of phishing schemes.
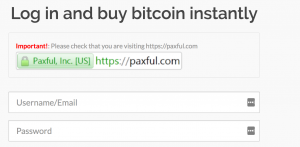
For instance, a recent article from Cisco Umbrella declared bitcoin wallet providers and other services are now the focal point of many fraud-based schemes. The article mentioned Kraken and Paxful users have already been targeted. Paxful even has a fidelity warning message to signal users that they are on the correct page. Luckily, most nefarious domains are suspended when the host realizes no name is registered or they receive complaints of phishing.
According to Cisco Umbrella, growth in these phishing schemes have risen in lockstep with the growth of bitcoin. The website even provided a pdf file with information regarding current phishing domains, which users should be aware of lest they have their bitcoin pick-pocketed. The Cisco blog explained,
We can also see that the amount of phishing attacks against bitcoin users keeps increasing. […] By pivoting around detected infrastructure, we found that it is not only used to host fraudulent Bitcoin domains, but a whole range of other nefarious ones as well.
Have you ever been the victim of a phishing attack geared to steal your bitcoin? Share your thoughts below!
Images courtesy of Shutterstock and umbrella.cisco.com
At News.Bitcoin.com all comments containing links are automatically held up for moderation in the Disqus system. That means an editor has to take a look at the comment to approve it. This is due to the many, repetitive, spam and scam links people post under our articles. We do not censor any comment content based on politics or personal opinions. So, please be patient. Your comment will be published.