Google has removed 49 cryptocurrency wallet browser extensions after a security researcher discovered they were stealing private keys. These Chrome extensions targeted users of crypto wallets, such as Ledger, Trezor, Jaxx, Electrum, Myetherwallet, Metamask, Exodus, and Keepkey.
Google Pulls 49 Cryptocurrency Wallet Browser Extensions Found Stealing Private Keys
This article was published more than a year ago. Some information may no longer be current.

49 Malicious Chrome Browser Extensions
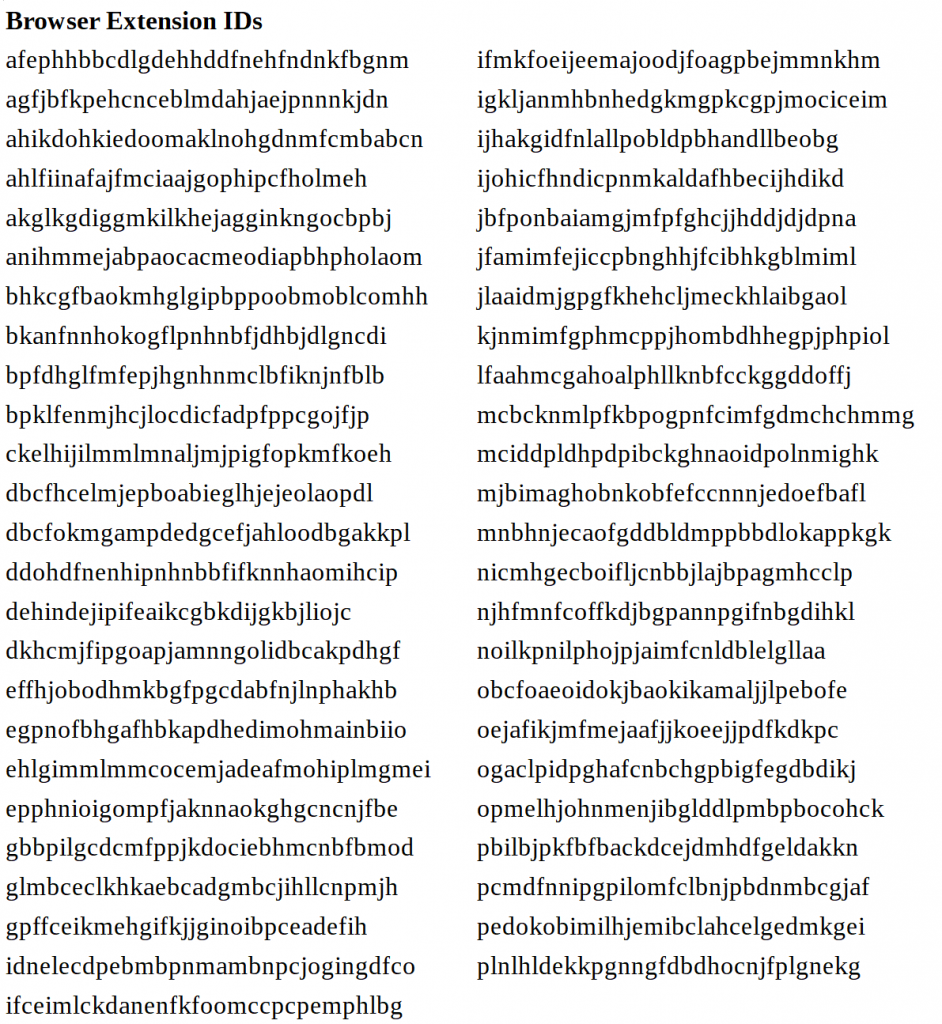
Security researcher Harry Denley revealed on Tuesday that 49 Chrome browser extensions have been stealing users’ cryptocurrency wallet private keys. Denley is the director of security at Mycrypto, an open-source tool for generating ether wallets and handling ERC20 tokens.
Posing as legitimate cryptocurrency wallet extensions, the 49 fake Chrome browser extensions contained malicious code that stole private keys, mnemonic phrases, and keystore files, the director described. They gathered data entered during different wallet configuration steps and sent them to one of the attacker’s servers or a Google Form. Some of these fraudulent browser extensions even had a network of fake users rating them with five stars or positive feedback. According to Denley, the extensions appear to be the work of one person or a group of people who are likely to be based in Russia.
The Targeted Cryptocurrency Wallets
Denley further revealed that the cryptocurrency wallets targeted by the 49 malicious Chrome browser extensions were Ledger, Trezor, Jaxx, Electrum, Myetherwallet, Metamask, Exodus, and Keepkey. He found that the most attacked wallet was Ledger, targeted by 57% of the malicious browser extensions. The second most targeted wallet was Myetherwallet (22%), followed by Trezor (8%), Electrum (4%), Keepkey (4%), and Jaxx (2%).
During his test, the security researcher sent funds to a few addresses and entered some secrets. He found that the funds sent were not automatically swept, concluding that the attackers were either only interested in high-value accounts or had to manually empty the addresses. Moreover, he noted that the malicious extensions started to hit the Google Chrome store in February slowly and rapidly increased releases through April. He added that they were reported to Google and removed within 24 hours.
What do you think about this? Let us know in the comments section below.