Wen Hao, CEO of Bither wallet, a Chinese mobile bitcoin wallet, said early Friday morning that the Bitclub pool (which has 4% of the total hashrate) launched a transaction malleability attack on the Bitcoin network during the night.
Bither CEO: Bitclub is Performing Segwit-related Attack Against Network
This article was published more than a year ago. Some information may no longer be current.

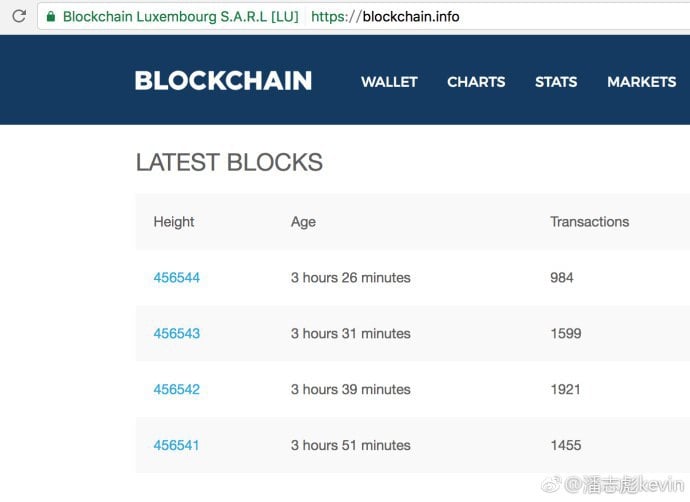
The attacks were evident in blocks mined by the pool in question; more specifically in block 456545 and 456552 – which led to a halt in Blockchain.info’s block monitoring updates. Some other blockchain monitors were still showing the correct block height (the latest blocks mined). Bitmain’s director of engineering also captured evidence of the ongoing attack, as witnessed in chinese chat rooms on the subject.
Also Read: Bitpay Confident in Bitcoin, But Raises Its Minimum Transaction Size
New Way To “Vote”?
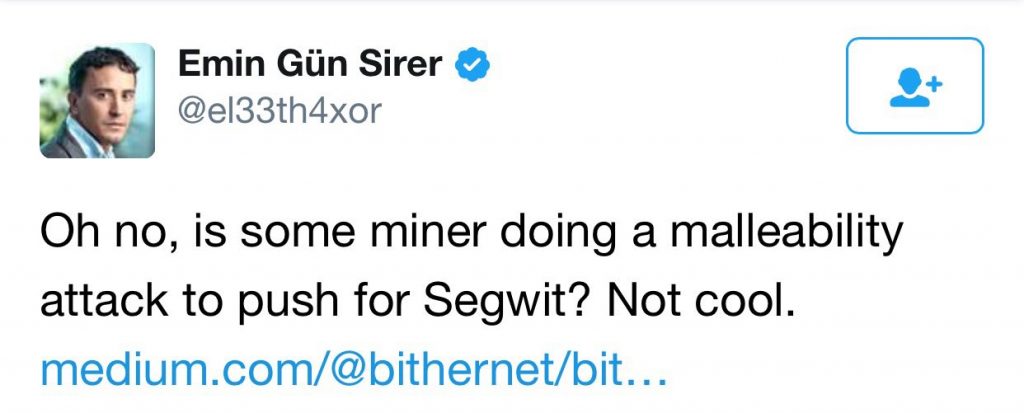
Some online chatter regarding the issue revolved around the idea that the attack is political; trying to influence developers and stakeholders to come to a solution to the so-called malleability issue (which Segwit is intended to solve).
Some even said it was a new way to signal preference for the proposed Segwit update. Bither’s Hao sent this message out in chat rooms and later also posted it on Reddit, and Medium;
“On March 10th at around 12:00 a user reported a double spend to us. We thought it was occasional. But when we looked into details, we found out it is a very well prepared attack by a pool on the bitcoin network.
BitClub (4%) was doing malleability attack. Without changing the content of the transaction, they managed to alter txid, by exploiting the symmetry characteristic of elliptic curves.
In the two blocks they mined, 456545 and 456552, they changed all the txid inside the blocks. In other words, they “double spent” all transactions. Blockchain.info, the most widely used blockchain explorer, is basically crashed during the attack event. Since block 456545, blockchain.info no longer received any new blocks.”
Updates To Follow
It’s still not exactly clear how the attack was performed. Investigations are under way, and some report the attack is still active. Blockchain.info, the most widely used blockchain explorer, basically crashed during the attack event. After block 456545, blockchain.info was no longer able to update on new blocks.
At this point in time, it seems unlikely this was unintentional, according to investigators. The “attack” involved not only extracting the signature, but also changing R to R’ in the elliptic curve cryptography.
Therefore, it is reasonable to assume the event was planned, prepared and programmed to achieve the intended outcome.
Later, another block (no. 456574) was also reported to contain “malleability attack” transactions.
Right now the Bitcoin community is discussing the subject heavily across forums and social media. Bitclub has not yet responded to the malleability attack accusations. Bitcoin.com will be following this story closely and will inform our readers of any new information that turns up.
What do you think about the malleability attacks? Let us know in the comments below.
Images courtesy of our correspondent in China, and Shutterstock.
Have you seen our new widget service? It allows anyone to embed informative Bitcoin.com widgets on their website. They’re pretty cool and you can customize by size and color. The widgets include price-only, price and graph, price and news, forum threads. There’s also a widget dedicated to our mining pool, displaying our hash power.