On August 2nd the Hong Kong-based Bitcoin exchange Bitfinex was compromised for roughly $70 million worth of Bitcoin. According to sources, the attacker managed to drain the exchange through its multi-signature security — gaining 120,000 BTC from the breach. Now the exchange is trying to reach out to the responsible party in an attempt to get its customers’ Bitcoin returned.
Bitfinex Seeks Communication With Bitcoin Thief
This article was published more than a year ago. Some information may no longer be current.

Also read: Walmart & IBM Improves Food Safety With Blockchain Tech
Negotiating With The Attacker
 The Bitfinex compromise shook the entire cryptocurrency community last summer. When the attack happened Bitcoin’s fiat value plummeted to $480 per BTC. Since then, its price has bounced back and Bitfinex is again fully operational.
The Bitfinex compromise shook the entire cryptocurrency community last summer. When the attack happened Bitcoin’s fiat value plummeted to $480 per BTC. Since then, its price has bounced back and Bitfinex is again fully operational.
As time passed, the company has provided additional information on reimbursing its customer base via its own issued BFX token.
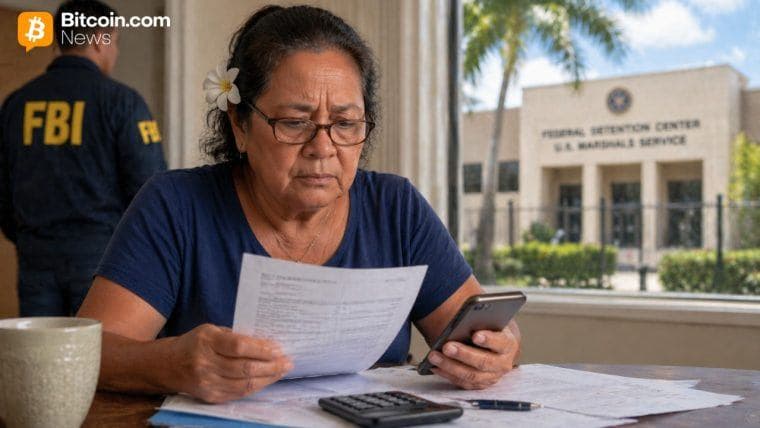
However there has been little information on how the exchange is working with authorities, or the investigation progress. We do know the FBI is aware of the attack though, as a Massachusetts resident has filed a complaint about the loss of $1.3 million USD in Bitcoin.
There are also many other complaints about how the exchange has not shared much information on the investigation. Now Bitfinex looks as though it is trying to negotiate with the attacker, stating on its blog:
We would like to have the opportunity to securely communicate with you. It might be possible to reach a mutually agreeable arrangement in exchange for an enormous bug bounty (payable through a more privacy-centric and anonymous way).— We have set up a dedicated email address recovery@bitfinex.com and a PGP key (id: 3DDF4814 | fingerprint: E7ED 6B5B 0172 2ECD 7F9D FCBC 6F19 A931 3DDF 4814), which can also be found on this public key server, to hopefully establish a secure line of communication with you.
Bitfinex Offers Anonymous Communication

The letter, written by CFO Giancarlo Devasini, says the company understands the attacker may be reluctant to communicate. So Bitfinex has offered some advice for the hacker to conceal his/her or the group’s identity. Devasini explained the attacker can use Tor and an anonymous email framework to keep anonymity. But in order to ensure communications are legitimate, Bitfinex also offered a public key to use paired with the attacker’s private key.
The exchange also offered communication through the Bitmessage platform. It supplied instructions to use the Bitcoin blockchain itself for discussion purposes. If the hacker chooses this communication route, the two parties can discuss within any one of the “2072 addresses currently holding the bitcoins in question.”
Devasini stated the company is “anxious” to hear back from the attacker, and it has an offer to make if discussions initiate. He explained, “our interest here is not to accuse, blame or make demands, but rather to discuss an arrangement that we think you will find interesting.”
The Probability of Negotiation Is Low
It is highly doubtful the attacker will communicate with Bitfinex, though, even with the anonymity methods provided. The attacker could very well assume law enforcement is working behind the scenes, using a cat-and-mouse technique. If the hacker decides to communicate it would be interesting to hear what the exchange has to offer.
Bitfinex still maintains its vow to pay customers back with the BFX token. It has initiated its first wave of reimbursements, but only 1.1812 percent of currently outstanding BFX tokens were redeemed. The company is hoping to negotiate with the person or group who stole the funds, but many believe the hope is basically unattainable.
Do you think the attacker will communicate with Bitfinex? Let us know in the comments below.
Images via Shutterstock, Linkedin, and the Bitfinex Blog.
Did you know Bitcoin.com is holding a blockchain conference in London this year? Our premiere event, Blockchain: Money, features the biggest innovators and executives in the industry. The event also takes place in the beautiful surroundings of 155 Bishopsgate, London on November 6-7, 2016. Reserve your tickets today!