Bitcoiners love Tor but the FBI has “updated” Rule 41 of the internet that could blacken Tor’s horizon. This means that unless Congress blocks it, using the anonymous browser could become illegal in the near future.
Bitcoiners Who Use Tor – Be Warned!
This article was published more than a year ago. Some information may no longer be current.

Also read: Blockstack to Help Microsoft Develop a Global ID Platform
Future of Tor in Jeopardy
Bitcoiners love the anonymity of Tor.
 The FBI hates it even though Tor is run by a government-backed American nonprofit. Even imperfect anonymity cripples the agency’s war on ‘crime’ – especially on victimless crimes like when people mind their own fiscal business. That’s why agents tried to interview one of Tor’s main software developers, Isis Agora Lovecruft (pseudo), over the last Thanksgiving holidays.
The FBI hates it even though Tor is run by a government-backed American nonprofit. Even imperfect anonymity cripples the agency’s war on ‘crime’ – especially on victimless crimes like when people mind their own fiscal business. That’s why agents tried to interview one of Tor’s main software developers, Isis Agora Lovecruft (pseudo), over the last Thanksgiving holidays.
Lovecruft jumped a fast plane to Germany to avoid being grilled for information that could have compromised the Tor system. A self-described “anarchist, hacker and physicist,” Lovecruft claims the FBI has been harassing her ever since.
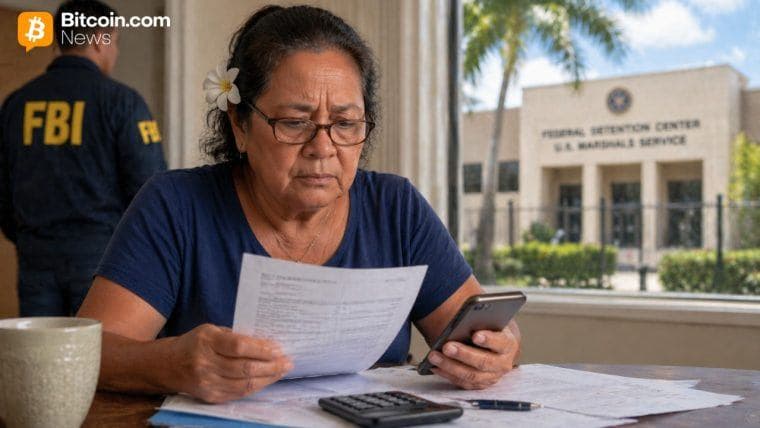
Now a game changer could further blacken Tor’s horizon…and that of Bitcoiners. On December 1, an “update” to Rule 41 of the Federal Rules of Criminal Procedure takes effect unless Congress blocks it. The info sounds dry as dust until you realize the change lets the FBI hack remotely into the phones and control the computers of Tor users. The target doesn’t have to commit a cybercrime; he may even be a victim of crime.
Gizmodo comments:
The new rule would allow the FBI to infect innocent people’s computer with malware in order to investigate cybercrime—even if their only connection to the crime is that they’re the victims. What could go wrong?”
If a person uses Tor, the FBI is empowered to get a discreet warrant that allows them to hack a computer and follow wherever the connection leads. In theory, with a single secret warrant, the agency could grab control of tens of thousands or millions of computers on a botnet.
What specifically is the “update” to Rule 41? Currently, the FBI needs to know the location of a computer suspected of ‘wrong-doing’ and then get a warrant in the proper jurisdiction. If they target a computer in Las Vegas, for example, they need a warrant from a Nevada judge. After December 1, any federal judge in America would be able to issue a warrant to allow the FBI to access an indefinite number of computers regardless of their locations.
All the FBI needs to claim is that the location of the computer has been intentionally concealed through use of technology – aka Tor. Legally-speaking, the agency’s surveillance may be restricted to the States but the ability to hack the globe would be out there, dangling. And when did a technicality prevent the FBI from surveillance? So many justifications are possible.
“Hacking a botnet leads you to unexpected connections; foreigners are committing crimes against Americans; we didn’t know the computer was in Switzerland, honest.”
Beyond US Borders
 Electronic Freedom Frontier (EFF) cautions, “Make no mistake: the Rule 41 proposal implicates people well beyond U.S. borders. This update expands the jurisdiction of judges to cover any computer user in the world who is using technology to protect their location privacy or is unwittingly part of a botnet. People both inside and outside of the United States should be equally concerned about this proposal.”
Electronic Freedom Frontier (EFF) cautions, “Make no mistake: the Rule 41 proposal implicates people well beyond U.S. borders. This update expands the jurisdiction of judges to cover any computer user in the world who is using technology to protect their location privacy or is unwittingly part of a botnet. People both inside and outside of the United States should be equally concerned about this proposal.”
Few people know about the “update.” It emerged from an obscure advisory committee that makes procedural changes in the rules governing all U.S. federal courts. For example, it determines the holidays on which the courts close. Then the Supreme Court passes the procedural change and a deadline onto Congress, where it is either blocked in time or automatically goes into effect.
Critics of Rule 41 pounce on the word “procedural.” And rightfully so. Only Congress has the authority to make a substantive change, which certainly describes the “update.” It gives the FBI massive new surveillance power and alters important powers of the court. For example, a court would lose the ability to throw out evidence due to law enforcement’s overreach into outside jurisdictions. There would be no jurisdiction outside the FBI’s reach.
And the grab is not likely to stop at Tor. Google’s legal director for law enforcement and information security warns:
Likewise, the change seemingly means that the limit on warrants is excused in any instance where a Virtual Private Network (VPN) is set up. Banks, online retailers, communications providers and other businesses around the world commonly use VPNs to help keep their networks and users’ information secure. A VPN can obscure the actual location of a network, however, and thus could be subject to a remote search warrant where it would not have been otherwise.
The EFF further explains, “It [the ‘update’] might also extend to people who deny access to location data for smartphone apps because they don’t feel like sharing their location with ad networks. It could even include individuals who change the country setting in an online service, like folks who change the country settings of their Twitter profile in order to read uncensored Tweets.”
In short, the probable cause is a desire for privacy for a warrant, and no one is sure which software or actions are included because the “update” is vague and broadly worded.
Push Back
 Happily, there is Congressional push back. H.R.5321 – the Stopping Mass Hacking Act (SMH or, in internet terms “Shaking My Head”) – was just introduced into the House. The Senate version, S.2952, is also in play.
Happily, there is Congressional push back. H.R.5321 – the Stopping Mass Hacking Act (SMH or, in internet terms “Shaking My Head”) – was just introduced into the House. The Senate version, S.2952, is also in play.
The bad news? Congress has only seven months to pass blocking legislation. Those seven months are filled by a need for hearings, summer breaks, holidays, RNC/DNC conventions, and the extreme distraction of an upcoming election.
Meanwhile, Bitcoiners and privacy-lovers should be on notice. Come December 1, a visit to Tor may be followed by a visit from the FBI …whether you know about the latter or not. For all practical purposes, Tor could become illegal.
What are your thoughts on this “update”? Do you think this will pass Congress? Let us know in the comments section below!
Images courtesy of nbcnews.com, simplyscratch.com, theregister.co.uk, gizmodo.com.au